| New findings about Usha Vance (nÉe Chilukuri) Usha and Vivek Ramaswamy are first cousins of the biotech Chilukuri sisters associated with the Pfizer, Astrazeneca, Blacksmith jab |
| British Pilgrims Society Facebook leader Peter Thiel is the $$$ tail that wags the JD Vance dog: State of the Nation |  |
Mar. 7, 2024—JD Vance's political grooming is too perfect.
JD Vance was plucked from Ohio State University that is controlled by British Pilgrims Society members at Battelle Memorial Institute and their MI6-C.I.A. stooges. Battelle Memorial Institute has very fat fingers in nine U.S. National Laboratories.
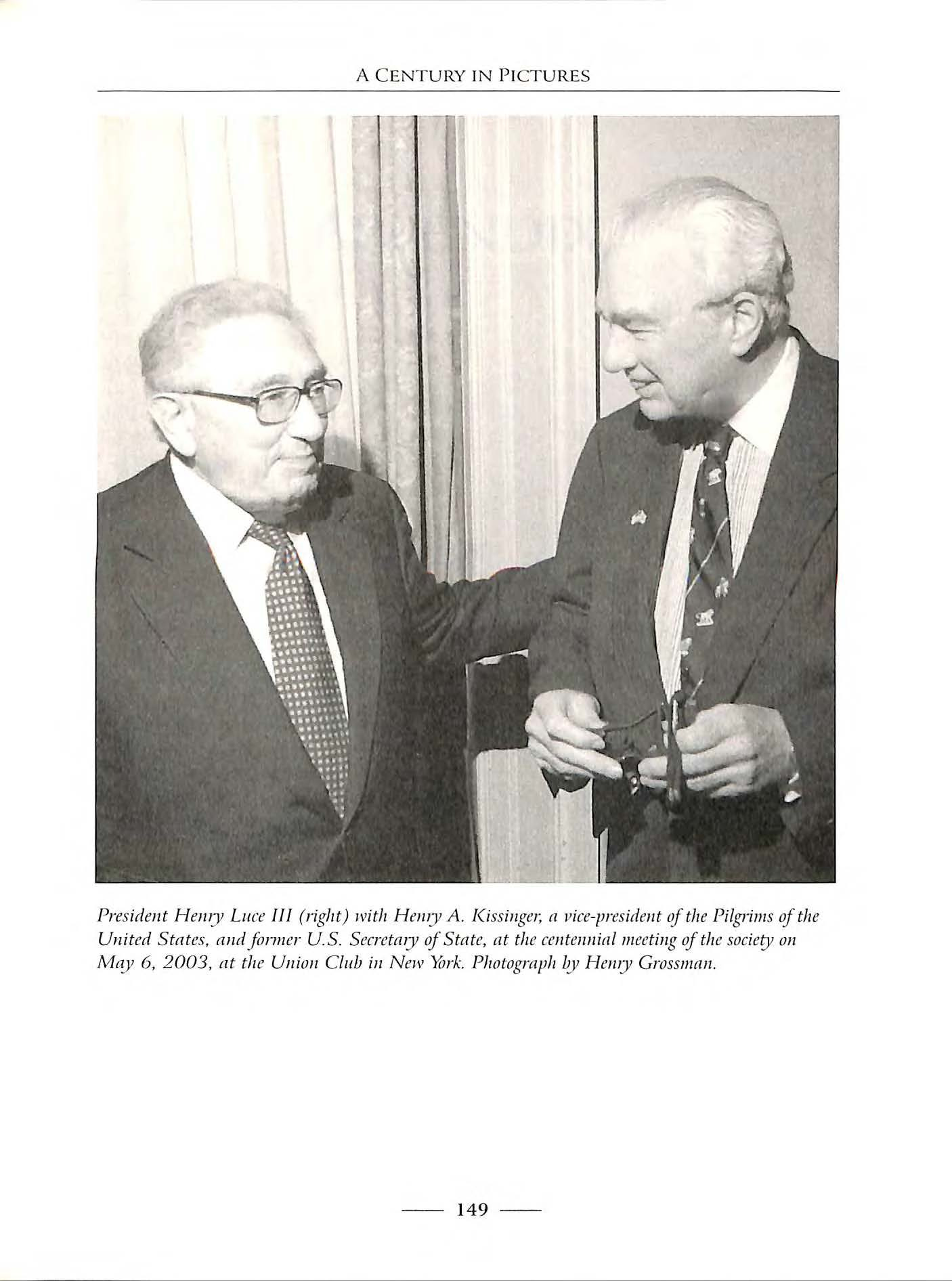
Longtime Battelle CEO and Ohio State University trustee president Jeffrey Wadsworth is British military background, and was embedded in the imperial plan to annex America. Wadsworth's signature is on documents proving his central role in the theft of social networking by Facebook from the real inventor, Leader Technologies, also from Columbus, Ohio. Wadsworth's smoking gun signature is containing in previous posts and below. It is evidence of his co-conspiracy to steal the social networking invention of his fellow-Columbus citizens and Ohio State alums at Leader Technologies.
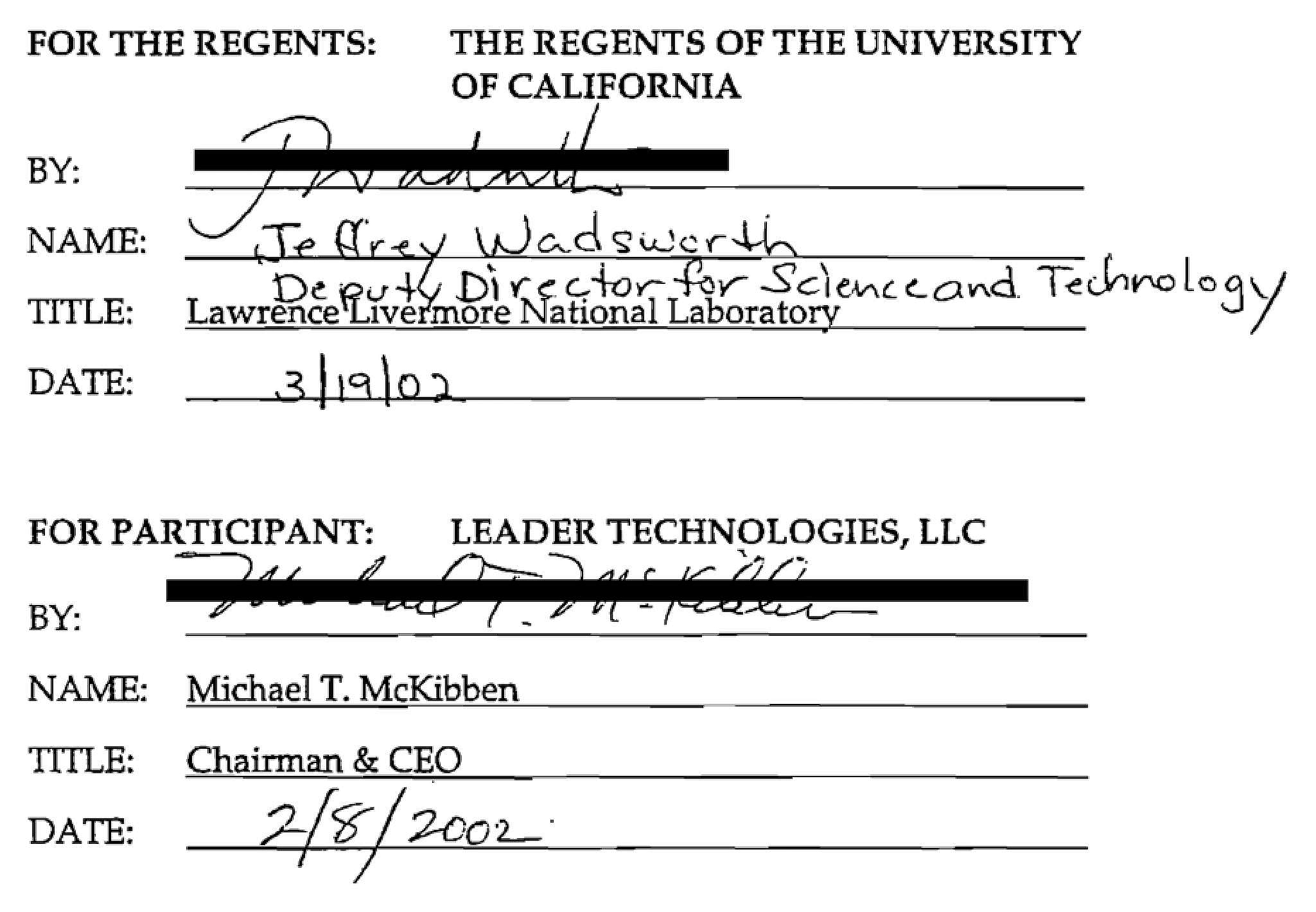
Note: On Aug. 29, 2002, IBM Eclipse Foundation released version 2.0.1 of its source code containing Leader Technologies' substantial innovations, claimed IBM copyrights and to this day fails to credit Leader Technologies' innovations as the basis for the Eclipse IDE. In the agreement cited above, attorney Chandler wrote himself into the agreement as the source code repository for the agreement. This is the code that came to be known as social networking. See Crimeline—The Greatest Financial Heist in History, today worth at least $10 trillion in market capitalization. In short, JD Vance is strapped to a rotting donkey carcass. What did he know, and when did he know it?

Meet Jeffrey Wadsworth, JD Vances' British "Five Eyes" Handler; His Lair: Ohio State University & Battelle Memorial Institute

Jeffrey NMI Wadsworth is the product of British military grooming by a career military father who traveled the globe (which often means he was a spy under cover with some other political or military day job). Jeffrey is a graduate of the University of Sheffield, a British Pilgrims Society military and technology-theft grooming stronghold.
In fact, the Sheffield Telegraph was one of the executive organizers of the First Imperial Press Conference, 1909 when modern propaganda, surveillance, and biowarfare was hatched.
Wadsworth did his postdoctoral research at Stanford University, another notorious C.I.A. finishing school. He worked for Lockheed Corporation--known to be controlled globally by the British Monarch's "Golden Share" of control.
Wadsworth became associate director of security at Lawrence Livermore National Laboratory (LLNL). This is where he first met Columbus, Ohio social networking inventor Leader Technologies. Wadsworth conspired with Leader's patent attorney, James P. Chandler, III to steal Leader's social networking invention and give Leader source code they stole to IBM, a co-collaborator at LLNL, and to Facebook via the IBM Eclipse Foundation. (PDF)
Wadsworth then moved to Columbus to become CEO at Battelle Memorial Institute where he coordinated intelligence efforts among DHS, Pacific Northwest Lab, the Department of Energy and Oak Ridge. No doubt feeling guilt for his thefts from real inventors, he retired into "philanthropy." See AIP interview of Jeffrey Wadsworth.
It must be noted that Central Ohio is becoming a network hub for the coming digital propaganda and slavery lock down. This is no doubt the result of former governor John Kasich and his Silicon Valley handler, Mark Kvamme, along with Battelle's resident British overlord Jeffrey Wadsworth. Ohio Babylonian Rādhānite oligarch Leslie Wexner has been conspiring for decades with Jeffrey Epstein. Victoria's Secret "soft porn" evidently recruited anorexic women and girls for decades, we believe. Facebook, Amazon and Google are each building top secret network operating centers. Even the ditch diggers on these projects are sworn to secrecy. We know because some have come forward. Intel is building a chip manufacturing plant in the Columbus suburbs. Ohio State is sponsoring MOOC, perhaps this biggest university education shift that no one seems to have heard off.
MOOC means Massive Open Online Course. MOOC will replace professors and teachers with online videos from the Ohio State MOOC hub. In so doing, a consistent Pilgrims Society curricula can be force fed to all secondary and higher education schools across the country and around the world. The Ohio Supercomputer Center, just off the Ohio State campus within a long walk of Battelle, is data location for the MOOC hub.
Governor John Kasich gave the MOOC data center computer contract to IBM. See Battelle IBM promo. He locked out Apple from the bid and destroyed the career of Ohio State's Marching Band director Jon Waters (HTML) because Waters was bringing unwanted world attention to Apple iPads and Ohio State's marching band innovations at the very same time that the British Pilgrims Society, through Jeffrey Wadsworth and Leslie Wexner, were making their moves to move Ohio State's data operations off campus and into the hands of IBM. Practically speaking there was no business need for the move. Ohio State's data center had plenty of excess capacity according to insiders. See Ohio State's president Michael Drake (an unwelcome California import) mired in personal conflicts of interest. (HTML)
Ohio State Marching Band Director Jon Waters' Career was sacrificed by Wadsworth's British Pilgrims handlers because Water's marching innovations brought unwanted attention to apple i-Pad and threatened to spoil the secret plan for IBM Eclipse to takeover Ohio State's data center and run globalist MOOC— facilitated by Wadsworth and Gov. Kasich.
Shame on the British Pilgrims Society, The City of London, The Ohio State University, Battelle Memorial Institute, Jeffrey Wadsworth, Les Wexner, Mark Kvamme, John Kasich, Joseph Steinmetz, and Michael Drake for attacking an innocent Jon Waters for your own inflated egos and megalomania. Karma is a beach.
It should be no surprise that in this Central Ohio moral cesspit, entrepreneur, inventor, and 4-year OSU Marching Band alum Michael McKibben, sensing the "idea stealing" culture in central Ohio, went silent and told no one what he was doing. He is notoriously known for being tight-lipped during his invention of social networking. Once invented, he made his first mistake of talking to Battelle Memorial Institute about teaming with him to implement his invention with IBM at Harvard. Zuckerberg was still in high school then. One can almost hear the giant sucking sound of intellectual property theft.

JD was hustled off to Yale Law for psychological indoctrination in the occult ways of the imperial British Empire. Note how Vanguard and State Street logos are pirate ships.
JD was placed in various venture capital companies associated with the British Pilgrims Society, MI6, C.I.A., IBM, Facebook, and the PayPal Mafia--all ultra leftist "progressives" and notorious "American-branch" handlers for the British Pilgrims Society financed by The City of London and their Rothschild gold and silver vaults.
- Peter Thiel (co-conspirator in the theft of social networking)
- James W. Breyer (co-conspirator in the theft of social networking)
- Eric Schmidt (co-conspirator in the theft of social networking)
- Marc Andreessen (co-conspirator in the theft of social networking)
- Steve Case (AOL)
- John Kasich (failed to protect inventor Leader Technologies; IBM co-conspirator)
- Mark Kvamme (Kasich's Silicon Valley handler in Ohio)
- Battelle Memorial Institute (co-conspirator in the theft of social networking)
- Jeffrey Wadsworth (co-conspirator in the theft of social networking)
- Robert Mercer
Do you see a "Republican" in this gaggle of handlers? No. They play Democrat by day, but are British Pilgrims Society drones out of The City of London by night. The Republican-Democrat (Uniparty) dichotomy is merely a propaganda construct to keep "the deplorables" from seeing their demonic British handlers.
These demons are busy annexing America into a reorganized imperial British corporatist Empire where a compliant monarchy has veto control (the "golden share") over all operations of all enterprises on the planet.
The CIA, FBI, NSA, US Army, Spawar (Navy), State Department, Judiciary, Congress are merely mopping up tools in their 200-year Cecil Rhodes plan for "one" world control through the British Pilgrims Society. Henry Kissinger, Paul Volcker, the Rockefeller cabal, Andrew Carnegie, David Sarnoff, were leading U.S. disciples. Now, look to Eric, Schmidt, James W. Breyer, Marc Andreessen, Stephen Schwarzman, Larry Fink, Jamie Dimon, and Peter Thiel, among others. American hero journalist Lillian Scott Troy discovered this Pilgrims Society strategy back in 1908 and did her best to warn us.
JD's pockets were filled with insider trading tips and investments in a dizzying array of early-stage companies funded by his handlers. See his outsized 2022 Financial Disclosure, like we would not notice the unreal gains and holdings. It is pure fairy land.
JD wrote a New York Times bestselling book, yet not one article in Yale Law Journal that he allegedly edited.
JD got A-list producer Ron Howard to produce his Netflix movie.
JD is elected to be an Ohio Senator on his first try.
A truly remarkable set of achievements for a person with no experience in anything he has been place in.
JD Vance is an evident cardboard cut out for his secret Pilgrims Society City of London handlers.
Ohio Senator JD Vance’s 2021 Financial Disclosure telegraphs insider trading. No inexperienced youth makes that many investments in such a wide range of industries without insider knowledge about which companies have the backing of the City of London merchant-banks (rolls up to the Rothschilds).
JD Vance is only 39-years old. Given the level of his political grooming since university, he has not had time to actually achieve anything besides being an evident mouthpiece for his handlers.
JD graduated Ohio State in 2007, then Yale Law where he edited Yale Law Review (a telltale British Pilgrims Society grooming job).
JD wrote a book casting himself as an Ohio/Kentucky hillbilly from the Rust Belt—Hillbilly Elegy: A Memoir of a Family and Culture in Crisis. Magically, the book became a The New York Times Best Seller.
Seriously? Plucked out of obscurity, a book about a boy raised in Appalachian Kentucky and Middletown, Ohio rockets to the top of the book and movie charts on its own energy? We don't think so.
He has evidently been groomed for such a time as this. Will Trump ever tell us the real story behind his selection?
Ohio Senator JD Vance’s 2021 Financial Disclosure telegraphs insider trading. No inexperienced youth makes that many investments in such a wide range of industries without insider knowledge about which companies have the backing of the City of London merchant-banks (rolls up to the Rothschilds).
JD Vance is only 39-years old. Given the level of his political grooming since university, he has not had time to actually achieve anything besides being an evident mouthpiece for his handlers.
JD graduated Ohio State in 2007, then Yale Law where he edited Yale Law Review (a telltale British Pilgrims Society grooming job).
JD wrote a book casting himself as an Ohio/Kentucky hillbilly from the Rust Belt—Hillbilly Elegy: A Memoir of a Family and Culture in Crisis. Magically, the book became a The New York Times Best Seller. Seriously? A book about an unknown boy raised in Appalachian Kentucky and Middletown, Ohio is promoted by The New York Times—a notorious mouthpiece for the British Pilgrims Society where they have never seen a bankers war they did not like. One reviewer said that while she enjoyed the writing skill of the Hillbilly Elegy ghost writer, she has been disappointed with JD Vance's incongruous conduct since the book—a notorious mouthpiece for the British Pilgrims Society where they have never seen a bankers war they did not like. One reviewer said that while she enjoyed the writing skill of the Hillbilly Elegy ghost writer, she has been disappointed with JD Vance's incongruous conduct since the book.
Venture Capital is called "Vulture Capital" for a reason
As a part of his evident grooming, JD has been placed at a number of venture capital firms. Numerous employees in these firms considered him a deal making lightweight. In one firm he did not close a single financing.
Venture capital firms ("VC" or "VCs") are becoming known for being mere feeder groups for the British Pilgrims Society in the The City of London with its access to an endless stream of deals, bottomless fiat currency, and a global network of Rothschild-controlled offshore banks.
"Venture capital" is a license to steal from young entrepreneurs and inventors. It is a confidence trick mill whereby, in most cases, the entrepreneur receives "tranches" of funding. Each tranche tightens the control of the "VC" over his prey, like a boa constrictor, until he gets control of the company and its creative output.
British Pilgrims Society "progressive" leftists in America (socialist Labour party in the UK) include Eric Schmidt, Darren Blanton, Peter Thiel, James Breyer Marc Andreessen, Steve Case, John Kasich, Mark Kvamme, Battelle Memorial Institute (Columbus, Ohio), Robert Mercer—all bandits of Facebook, Palantir, LinkedIn, Instagram, Gmail, YouTube, and Paypal. These men evidently pull JD’s chain.
Photo: Venture capitalists taking control of human creativity

"Evil is created when money makes money with no human effort."
Venture capital is No Risk insider trading for MI6, Admiralty, DARPA, DoD, In-Q-Tel, SERCO, QinetiQ, Highlands Group, Wellcome Trust UK, Rothschild Asset Management, The City of London merchant-banks.
"Thou shalt not steal."
Usury is war against your fellow human being.
Lord Victor Rothschild created the biowarfare industry in 1973 using venture capital and infinite City of London usury profits.
Laughably, Hollywood then made a film about JD being a hillbilly from the Rust Belt to cement his Ohio-based bonafides as a hick that the left and the right coasts must take care off, like a puppy. The movie was produced by Ron Howard who was surely well-paid to concoct a heart-tugging yarn. If you think it is true, then examine your reactions and emotions, because you have been played.
JD Vance's Ohio Senate Seat is the best politics that the Pilgrims Society in the city of london can buy
JD was then placed in the US Senate in 2022, funded by his Pilgrims Society financiers. Magical.
No-experience freshman Ohio Senator JD Vance was then placed on six (6) important Senate Committees—to vote the way of his handlers, evidently.
Wikipedia, like a good little lapdog, waxes eloquent on 14 pages about JD’s political positions which, magically, match the polling of conservatives, so he learns how to mouth the right words, while he turns the knife slowly in the backs of conservatives.
Imagine that, JD Vance has learned his lines well. He's an actor who can talk a good conservative game founded on daily polling, but is in reality controlled opposition.
$1500/hr. JD Vance lawyers & accountants prepared this unsearchable mess
Another "tell" confirming JD's grooming is his 2022 Senate Financial Disclosure which he filed late. See Senator J.D. Vance. (Nov.24, 2021). 2021 Financial Disclosures. U.S. Senate
Besides the unreal bloated contents, the digital format of the 24-page file that he submitted was evidently doctored to prevent search engines from picking embarrassing content.
It is a PDF file that was formatted from Excel using an obviously intentionally discombobulated cell structure that only a criminal lawyer would cook up. It randomly merged some cells (to thwart cut and paste). It inserted 20-30 unused columns and rows, also thwarting cut and paste. It overlapped embarrassing entries over header text making it nearly impossible to read, but looking like scanning errors.
Anonymous Patriots have totally de clawed the financial disclosure document that is linked herein.
We The People need to disband the U.S. Office of Government Ethics (OGE) for allowing JD Vance and others to hide their unflattering reports in a flurry of formatting nonsense.
Can America unchain herself from the Pilgrims Society’s 24-pt. plan to ANNEX AMERICA? |
 |
We did not heed Lillian Scott Troy’s warnings in 1913. We let her be deported and robbed by England without protest. Will we listen to her now, 111 years later? Time will tell. |
|
"Would Ānnex ĀmericĀ."
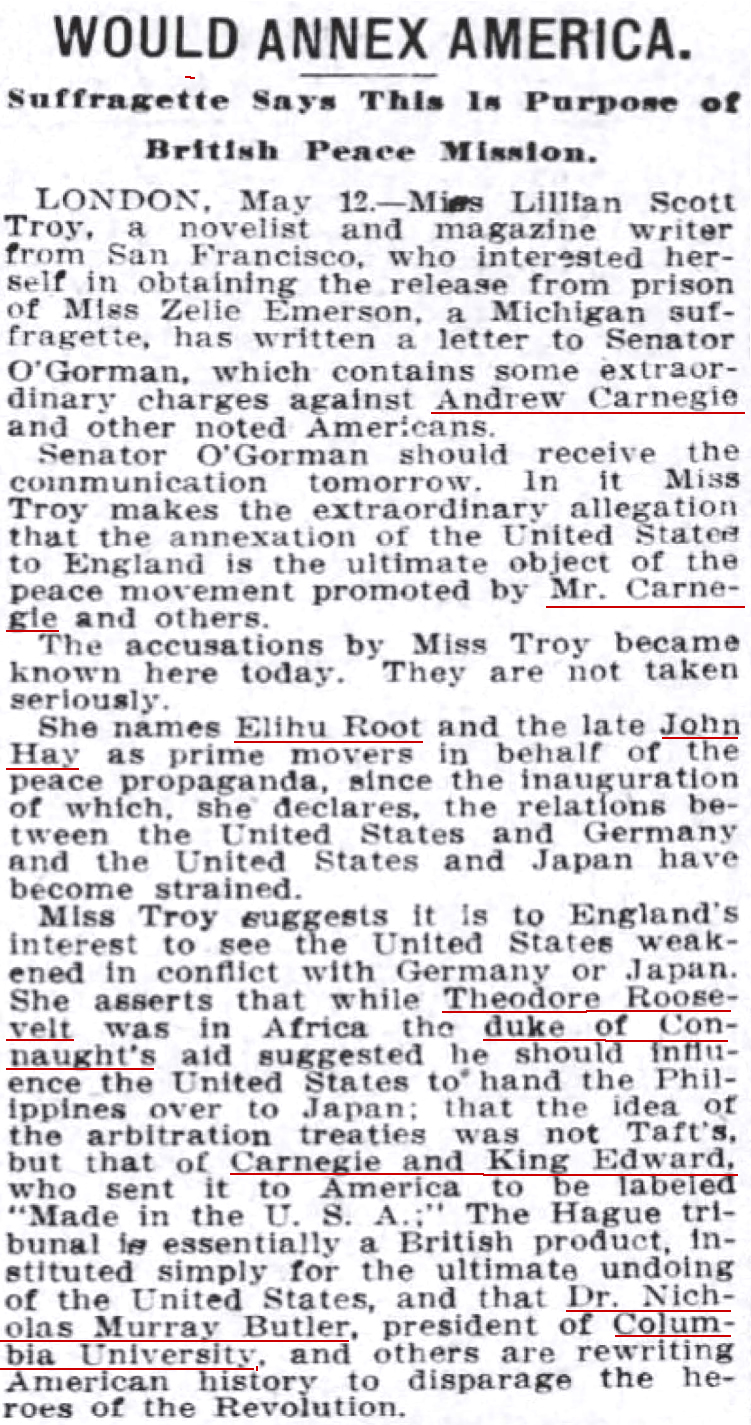
Fig. 7—Editor: (May 13, 1913). Would Annex America [says Lillian Scott Troy], p. 20. The Commercial Appeal (Memphis, Tennessee).
Note: Columbia University president Nicholas Murray Butler served as president of the Pilgrims Society of the United States "branch" from 1903-1945. He oversaw the organizing of the British First Imperial Press Conference, 1909, oversaw the recruitment of Franklin D. Roosevelt, David Sarnoff (RCA, NBC), J. Edgar Hoover (FBI), Anglican Bishop Henry C. Potter into the Pilgrims Society.
Elihu Root was co-founder of the Pilgrims Society (1902); former U.S. Secretary of War (1899-1904); U.S. Secretary of State (1905-1909); NY U.S. Senator (1909-1913); founding president, Carnegie Endowment for International Peace (1910); Nobel Prize (1912); founder, Council on Foreign Relations (1918). He was also personal attorney to J.P. Morgan and Andrew Carnegie.
John Hay was U.S. Ambassador to the Court of St. James where he promoted annexation of America by Britain. He once described (banker) war "as necessary as it is righteous" and described another war as "a splendid little war"--he was a Pilgrims Society merchant-banker warlord par excellence.
American heroine Lillian Scott Troy
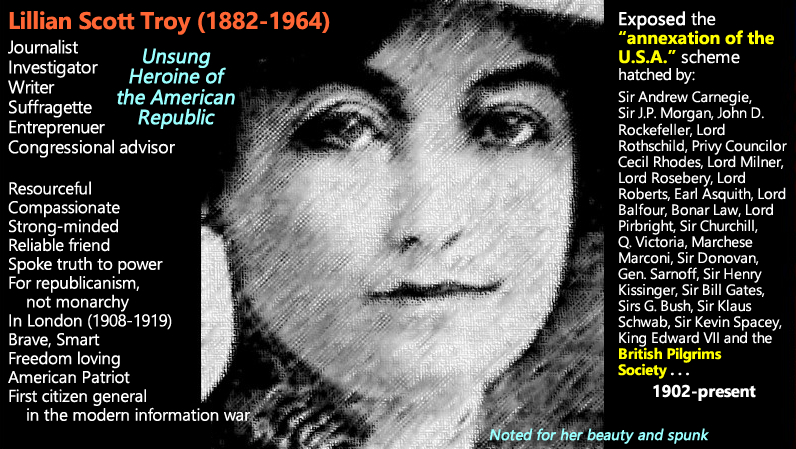
Fig. 8—Editor. (May 13,1913). Would Annex America [says Lillian Scott Troy], p. 20. The Commercial Appeal (Memphis, Tennessee).
. . . "[T]he idea of the arbitration treaties was not Taft’s, but that of [Andrew] Carnegie and King Edward [VII] who sent it to America to be labeled “Made in the U.S.A.;” The Hague tribunal is essentially a British product, instituted simply for the ultimate undoing of the United States, and that Dr. Nicholas Murray Butler, president of Columbia University, and others are rewriting American history to disparage the heroes of the Revolution." (Emphases added.)
Who was American Nicholas Murray Butler? Click this link to read his full Pilgrims Society-Columbia University biography. Click here for a PDF.
* * *
On Apr. 25, 2019, then President Trump was served official notice, as the chief executive, that the U.S. government violated the property rights of social networking inventor Leader Technologies--the First Amended Miller Act Notice.
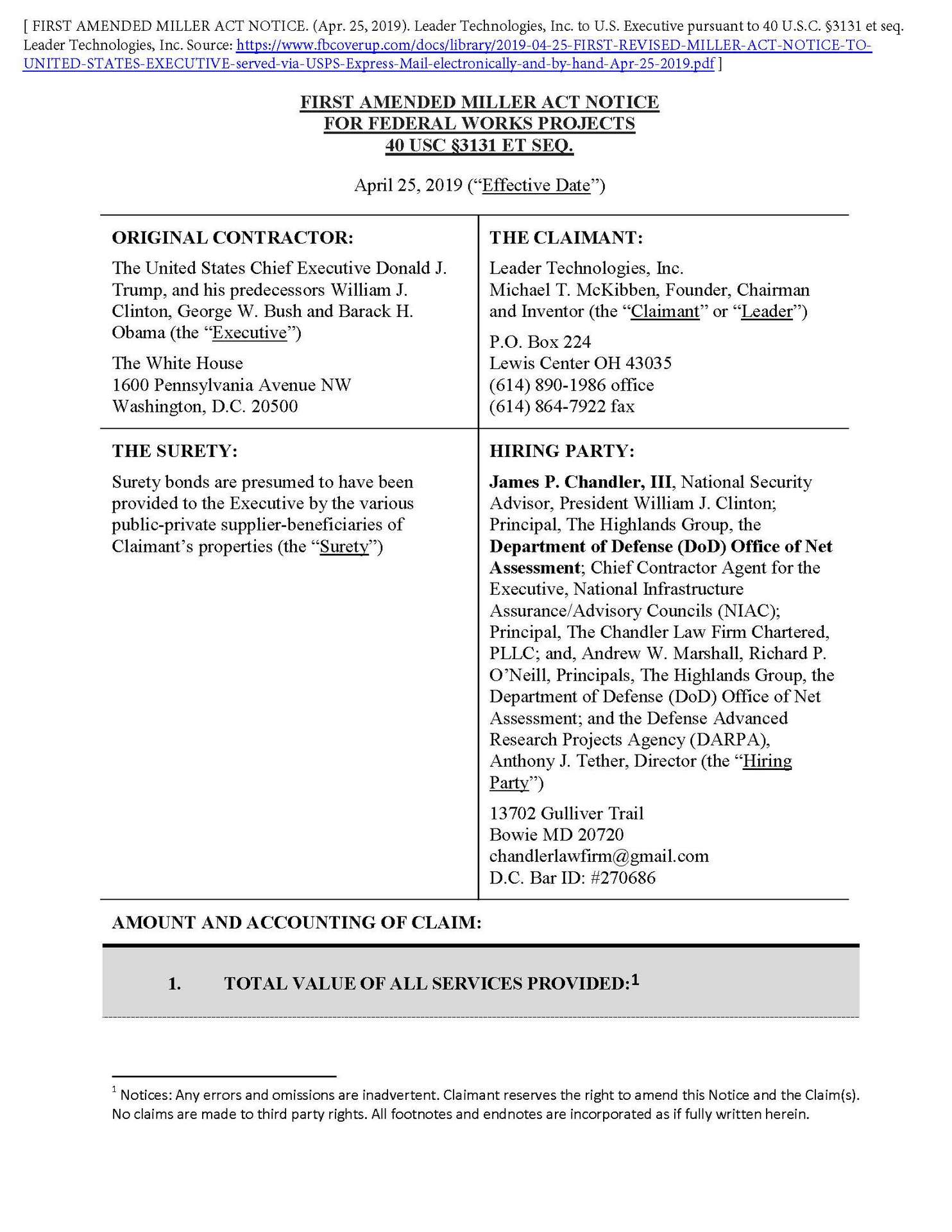
Fig. 9—FIRST AMENDED MILLER ACT NOTICE. (Apr. 25, 2019). Leader Technologies, Inc. to U.S. Executive pursuant to 40 U.S.C. §3131 et seq. Leader Technologies, Inc.
Truth Social has parked its Ponzi scheme on Michael McKibben's patented technologies without paying a license fee. Despite having proof that Trump (or at least certain advisors) received formal notice of the theft, these facts are not disclosed to Trump's prospective investors in their SEC filing. This is evident fraud by at least Trump's auditors, securities lawyers, and advisors. Was he being further set up or is he in on this fraud? Time will tell. Given the results of the latest Alvin Bragg show trial, Trump's enemies appear to stop at nothing to compromise the advisors around Trump.

Trump knows all about the theft of social networking. Leader sent him hundreds of Fifth Amendment demands by its shareholders. It was delivered by senior staffers from Rep. Jim Jordan's office. We note that the Truth Social SEC disclosures discombobulate their position relative to potential infringed property. The wording is evidently intended to absolve Trump of any potential liability for a supposed lack of knowledge of his infringement of Leader Technologies social networking inventions.
Rep. Jim Jordan's staff hand delivered the Miller Act Notice to the white House

It is the same Uniparty pattern that we have discovered with Ron DeSantis, Sarah Huckabee-Sanders, Glenn Youngkin, Gavin Newsom, J.D. Vance (Silicon Valley’s man), Vivek Ramaswamy (Soros Big Pharma man), Candice Owens, and RINO Nikki Haley (see her 52-page Wikipedia screed.)
With each profile, the Uniparty paymaster has a different face, but all roads eventually lead back to the same The City of London Babylonian Rādhānite merchant-bankers in the British Pilgrims Society—the real face of the “deep state.” See more on the Babylonian Rādhānites below.

Five Eyes, ANCIB(US)-ANCICC(UK). (Mar. 11, 1946). DAY 1: TOP SECRET CREAM, Inauguration Meeting, U.S. - British Signal Intelligence Technical Conference, March 11, 1946, DOCID: 2959299, REF ID: A2666693, National Archives Ref: HW-80-5, PDF p. 108. NSA.
Note: British MI6 is still redacting many of the names on their delegation, thus committing espionage against the United States in 1946, and still today.
Who Pulls JD Vance's Chain?
The British Pilgrims Society through The City of London and the Babylonian Rādhānite (Radknights) merchant-banker pagans who control the British Crown.
Their flunkies doing their bidding in the USA are British Spy No. 7 Alexander Hamilton’s American banks, notably JPMorgan, Bank of America, Bank of New York Mellon, State Street along with asset managers like BlackRock, Fidelity, T. Rowe Price and Vanguard, who are controlled by the British Crown and the Rothschilds in the City of London via the Monarch’s “Golden Share.”
Don’t believe that the British run America? Just look at the false flag they are trying to orchestrate in Poland right now. Poland is historically one of the favorite choke points of the British Empire to try and take down Russia to seize control of Russia’s 11 times zones of resources, again. When will we learn?
Tragically, Kristi Noem's handlers are the ones attempting to depopulate us folks.
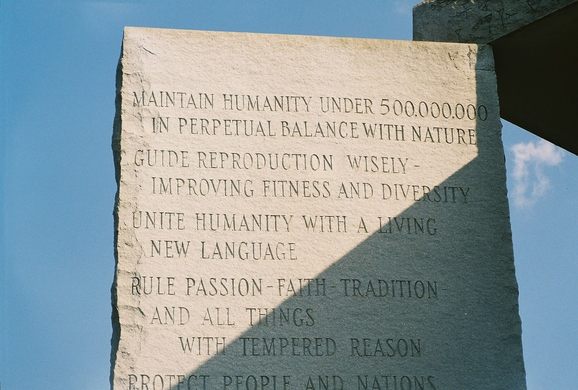
GOD-LIKE GENOCIDAL TEXT: "MAINTAIN HUMANITY UNDER 500,000,000 IN PERPETUAL BALANCE WITH NATURE"

William was Norman (French). The Babylonian Rādhānite (demon-worshipping pagans who claimed to be Jews for more than three millennia) already had an extensive banking and trade network through Europe and Middle East, Scandinavia and Africa to China.
The Rādhānite merchant-bankers were forced to flee Babylon (renamed Baghdad) ahead of the armies of the Muslim Seljuk Turks in 1055 A.D.—just 11 years earlier. They fanned out along their extensive network of merchant-banking trading post across the known world.
“And Jesus entered the temple and drove out all who sold and bought in the temple, and he overturned the tables of the money-changers and the seats of those who sold pigeons. He said to them, It is written, ‘My house shall be called a house of prayer,’ but you make it a den of robbers.'” Matthew 21:12-13.
“Synagogue of Satan”
“Behold, I will make them of the synagogue of Satan, which say they are Jews, and are not, but do lie; behold, I will make them to come and worship before thy feet, and to know that I have loved thee.” Revelation 3:9.
In the process, they rebranded themselves as “Ashkenazi Jews.” They had called themselves Jews for millennia while in Babylon, but they had created their unique pagan version that followed the Talmud, Yiddish, and rabbis, rather than the Torah, Hebrew, and Prophets.
The Babylonian Empire codified debt slavery by sanctioning usury (charging interest on the loan of money) in the Code of Hammurabi (1755–1750 BC). They put fake Jews in charge of these practices.
While the Prophets Ezekiel and Daniel ca. 600 BC were decrying usury, exiled "Jews" like the Egibi and Marushu banking families, who had so intermixed with Persians that their Jewishness had vanished, were assigned the task of running all aspects of the Babylonian economy, including Silk Road commerce from Britain to China, leveraging Solomon's Gold, banking, finance, intelligence, propaganda, engineering, agriculture, and trade.
The Babylonian Empire worshipped demon gods who demanded child sacrifice and debt slavery, including Mammon, Moloch, Asmodeus, Ba’al, Baphomet, Beelzebub, Behemoth, Ishtar, Legion, Leviathan, Lucifer, Mammon, Marduk, Moloch, Pazuzu, Satan, Agrat bat Maḥlat, Alu, Alukah, Asherah, Ashmodai, Astarte, Azazel, Belial or Beliar, Bel-Marduk, Chemosh, Dagon, Deber, Dever, Ekimmu, Gallu, Horon, Ilu Limnu, Keṭeb, Kotar Hosis, Labartu, Labartu, Lamashtu, Lilith, Lilu, Lotape, Mavet, Nahar, Nergal, Ninisina, Pentalpha, Rabisu, Reshef, Resheph, Resheph, Samael, Shachar, Shalem, Shamḥazai, Shedim, Shedim, Tannin, Tiamat, Tirosch, Yoḥane bat Reṭibi, and others.
King Solomon's 600 wives and 300 concubines eventually lured him into building temples to and worshipping these Babylonian demon gods. This is evidently when the Babylonian Rādhānite took full control of Solomon's Gold that had been carted off to Babylon. Then, shipped to The City of London ca. 1067 AD.


* * *
Tell the Synagogue of Satan
Jesus Christ: "Get behind me, Satan."
—Matthew 16:23
Described above is abject immorality on the part of the British Pilgrims Society and their Babylonian synagogue of satan demons.
Morality must win the day.
"Repent, for the kingdom of heaven is at hand."
The Gospel of St. Matthew 4:17.
Bookmark: #miller-act-notice | https://tinyurl.com/5btymkk2

Leader Technologies, Inc. sent their FIRST AMENDED MILLER ACT NOTICE to President Trump (the then-current President) It is a contract demand for the U.S. Treasury to pay them for the federal government's 18-year theft of their social networking inventions. These inventions were stolen by Major General James E. Freeze (US Army, ret.) and Leader's patent attorney James P. Chandler, III, on behalf of Andrew W. Marshall and the Department of Defense Office of Net Assessment, and the Pilgrims Society who steal and weaponize inventions for continuous war making and enrichment of fascist insider military-industrial corporations.
Patriots are encouraged to help get this First Amended Miller Act Notice to President Trump and past the Praetorian Guard. See American Intelligence Media republish of the Leader Miller Act Notice.
Return to return to the beginning of this post.
Notices: This post may contain opinion. As with all opinion, it should not be relied upon without independent verification. Think for yourself. Photos used are for educational purposes only and were obtained from public sources. No claims whatsoever are made to any photo.
Comment
Click "N comments:" on the line just below this instruction to comment on this post. Alternatively, send an email with your comment to afi@leader.com and we'll post it for you. We welcome and encourage anonymous comments, especially from whisteblowers.

 e.g. "IBM Eclipse Foundation" or "racketeering"
e.g. "IBM Eclipse Foundation" or "racketeering"